Hi!!
We checked mgm and fst configuration and permission and ownership of derectories. And restart all eos services.
but, I can’t pass the open write/read/delete test. 
testSE ALICE::Hiroshima::EOS
>testSE ALICE::Hiroshima::EOS
ALICE::HIROSHIMA::EOS
Open write test: could write, (NOT OK), please check authorization configuration
Open read test: reading worked (NOT OK) please check authorization configuration
Open delete test: delete worked (NOT OK)
Authenticated write test: could write (expected)
Authenticated read: file read back ok (expected)
Authenticated delete: delete worked ok (expected)
Space information:
Path: /
Total: 1.44 PB (LDAP setting: 1582914076672)
Free: 1.434 PB
Used: 5.479 TB
Chunk: 64 GB
Version: Xrootd 5.8.4
LDAP information:
SE: seName: ALICE::HIROSHIMA::EOS
seNumber : 428
seVersion : 0
qos : [test]
seioDaemons : root://eos.aligrid.hiroshima-u.ac.jp:1094
seStoragePath : /
seSize: : 1582914076672
seUsedSpace : 33
seNumFiles : 3
seMinSize : 0
seType : File
exclusiveUsers : []
seExclusiveRead : []
seExclusiveWrite : []
options: {}
mgm services still dont read TkAuthz.Authorization. There are nothing about authorization on the mgm master log file.
[root@grid04 ~]# tail -n 100 /var/log/eos/mgm/xrdlog.mgm | grep XrdAliceTokenAcc
Any advice would be appreciated.
I attached current setting.
Thanks in advance.
Takuma
Details:
stat output relating to TkAuthz.Authorization
[root@grid04 ~]# stat /etc/grid-security/xrootd/TkAuthz.Authorization
File: /etc/grid-security/xrootd/TkAuthz.Authorization
Size: 285 Blocks: 8 IO Block: 4096 regular file
Device: fd00h/64768d Inode: 201597734 Links: 1
Access: (0600/-rw-------) Uid: ( 2/ daemon) Gid: ( 2/ daemon)
Context: system_u:object_r:etc_t:s0
Access: 2025-09-04 01:09:13.455865542 +0900
Modify: 2025-09-04 01:08:49.067335343 +0900
Change: 2025-09-04 01:09:03.011061829 +0900
Birth: 2025-09-04 01:08:49.067335343 +0900
[root@grid04 ~]# stat /etc/grid-security/xrootd
File: /etc/grid-security/xrootd
Size: 72 Blocks: 0 IO Block: 4096 directory
Device: fd00h/64768d Inode: 201566276 Links: 2
Access: (0700/drwx------) Uid: ( 2/ daemon) Gid: ( 2/ daemon)
Context: system_u:object_r:etc_t:s0
Access: 2025-09-04 03:56:15.757465443 +0900
Modify: 2025-09-04 01:08:49.067854156 +0900
Change: 2025-09-04 01:08:49.067854156 +0900
Birth: 2025-05-10 17:04:24.781787639 +0900
[root@grid04 ~]# stat /etc/grid-security
File: /etc/grid-security
Size: 112 Blocks: 0 IO Block: 4096 directory
Device: fd00h/64768d Inode: 167773889 Links: 5
Access: (0755/drwxr-xr-x) Uid: ( 0/ root) Gid: ( 0/ root)
Context: system_u:object_r:etc_t:s0
Access: 2025-09-04 01:08:14.869966547 +0900
Modify: 2025-08-28 17:04:23.672717205 +0900
Change: 2025-08-28 23:43:33.549857350 +0900
Birth: 2025-05-10 17:03:39.546607021 +0900
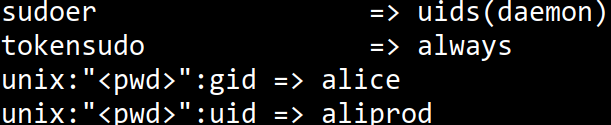
eos vid setting
[root@grid04 ~]# eos vid ls
https:"<pwd>":gid => root
https:"<pwd>":uid => root
publicaccesslevel: => 1024
sss:"<pwd>":gid => root
sss:"<pwd>":uid => root
sudoer => uids(daemon)
tokensudo => always
unix:"<pwd>":gid => alice
unix:"<pwd>":uid => aliprod
This is configuration files for eos seicvices.
[root@grid04 ~]# cat /etc/xrd.cf.mgm | grep sec.protocol
sec.protocol unix
sec.protocol sss -c /etc/eos.keytab -s /etc/eos.keytab
xrd.cf.mgm
###########################################################
set myName = ALICE::Hiroshima::EOS
all.sitename ALICE::Hiroshima::EOS
###########################################################
xrootd.fslib libXrdEosMgm.so
xrootd.seclib libXrdSec.so
xrootd.async off nosf
xrootd.chksum adler32
###########################################################
xrd.sched mint 8 maxt 256 idle 60
xrd.timeout hail 30 idle 300 kill 20 read 20
###########################################################
# caused this line?
all.export / nolock
all.role manager
###########################################################
xrd.port 1094
###########################################################
oss.fdlimit * max
###########################################################
# UNIX authentication
sec.protocol unix
# SSS authentication
sec.protocol sss -c /etc/eos.keytab -s /etc/eos.keytab
sec.protbind localhost.localdomain sss unix
sec.protbind localhost sss unix
sec.protbind * only sss unix
###########################################################
mgmofs.fs /
mgmofs.targetport 1095
mgmofs.centraldrain true
mgmofs.authlib /usr/lib64/libXrdAliceTokenAcc.so
mgmofs.authorize 1
alicetokenacc.multiprocess 32
alicetokenacc.truncateprefix /eos/hu/alice
alicetokenacc.noauthzhost localhost
#alicetokenacc.noauthzhost localhost.localdomain
# VOBOX
alicetokenacc.noauthzhost grid01.aligrid.hiroshima-u.ac.jp
# MGMs
#alicetokenacc.noauthzhost grid04.aligrid.hiroshima-u.ac.jp
#alicetokenacc.noauthzhost grid05.aligrid.hiroshima-u.ac.jp
#alicetokenacc.noauthzhost grid06.aligrid.hiroshima-u.ac.jp
# FSTs
#alicetokenacc.noauthzhost nfs11.aligrid.hiroshima-u.ac.jp
#alicetokenacc.noauthzhost nfs12.aligrid.hiroshima-u.ac.jp
#alicetokenacc.noauthzhost nfs13.aligrid.hiroshima-u.ac.jp
###########################################################
#mgmofs.trace all debug
# this URL can be overwritten by EOS_BROKER_URL defined in /etc/sysconfig/eos
mgmofs.broker root://eos.aligrid.hiroshima-u.ac.jp:1097//eos/
# this name can be overwritten by EOS_INSTANCE_NAME defined in /etc/sysconfig/eos
mgmofs.instance eoshu
# configuration, namespace , transfer and authentication export directory
mgmofs.configdir /var/eos/config
mgmofs.metalog /var/eos/md
mgmofs.txdir /var/eos/tx
mgmofs.authdir /var/eos/auth
mgmofs.archivedir /var/eos/archive
mgmofs.qosdir /var/eos/qos
# report store path
mgmofs.reportstorepath /var/eos/report
# this defines the default config to load
mgmofs.autoloadconfig default
mgmofs.autosaveconfig true
# QoS configuration file
# mgmofs.qoscfg /var/eos/qos/qos.conf
###########################################################
# Config Engine Configuration
mgmofs.cfgtype quarkdb
# this has to be defined if we have a failover configuration via alias - can be overwritten by EOS_MGM_ALIAS in /etc/sysconfig/eos
mgmofs.alias eos.aligrid.hiroshima-u.ac.jp
###########################################################
# Set the FST gateway host and port
# mgmofs.fstgw someproxy.cern.ch:3001
#-------------------------------------------------------------------------------
# Configuration for the authentication plugin EosAuth
#-------------------------------------------------------------------------------
# Set the number of authentication worker threads running on the MGM
mgmofs.auththreads 16
# Set the front end port number for incoming authentication requests
#mgmofs.authport 15555
# By default we listen only on localhost connections - set to 0 if you want to allow remote access
#mgmofs.authlocal 1
#-------------------------------------------------------------------------------
# Set the namespace plugin implementation
#-------------------------------------------------------------------------------
mgmofs.nslib /usr/lib64/libEosNsQuarkdb.so
# Quarkdb custer configuration used for the namespace
mgmofs.qdbcluster grid04.aligrid.hiroshima-u.ac.jp:7777 grid05.aligrid.hiroshima-u.ac.jp:7777 grid06.aligrid.hiroshima-u.ac.jp:7777
mgmofs.qdbpassword_file /etc/quarkdb.pass
#-------------------------------------------------------------------------------
# Configuration for the MGM workflow engine
#-------------------------------------------------------------------------------
# The SSI protocol buffer endpoint for notification messages from "proto" workflow actions
#mgmofs.protowfendpoint HOSTNAME.2NDLEVEL.TOPLEVEL:10955
#mgmofs.protowfresource /SSI_RESOURCE
# Use gRPC?
# mgmofs.protowfusegrpc true
if exec xrootd
xrd.protocol XrdHttp:8443 libXrdHttp.so
http.exthandler EosMgmHttp libEosMgmHttp.so eos::mgm::http::redirect-to-https=1
http.trace false
# host cert required !!!
http.exthandler xrdtpc libXrdHttpTPC.so
xrd.tls /etc/grid-security/hostcert.pem /etc/grid-security/hostkey.pem
xrd.tlsca certdir /etc/grid-security/certificates/
# X509 Stuff
# http.secxtractor libXrdVoms.so
# http.gridmap /etc/grid-security/grid-mapfile
# Macaroons
# mgmofs.macaroonslib libXrdMacaroons.so libXrdAccSciTokens.so
# macaroons.secretkey /etc/eos.macaroon.secret
# macaroons.trace all
fi
xrootd.monitor all flush 60s window 30s dest files info user grid01.aligrid.hiroshima-u.ac.jp:9930
[root@nfs11 ~]# cat /etc/sysconfig/eos_env | grep EOS_FST_NO_SSS_ENFORCEMENT=1
EOS_FST_NO_SSS_ENFORCEMENT=1
xrd.cf.fst
###########################################################
set MGM=eos.aligrid.hiroshima-u.ac.jp
###########################################################
###########################################################
set myName = Hiroshima
all.sitename ALICE::Hiroshima::EOS
xrootd.fslib -2 libXrdEosFst.so
xrootd.async off nosf
xrd.network keepalive
xrootd.redirect $(MGM):1094 chksum
# Specify when threads are created, how many can be created, and when they should be destroyed.
# https://xrootd.web.cern.ch/doc/dev57/xrd_config.htm#_Toc171719950
xrd.sched mint 16 avlt 24 idle 60 maxt 512
# Set timeout parameters for incoming connections
# https://xrootd.web.cern.ch/doc/dev57/xrd_config.htm#_Toc171719953
xrd.timeout hail 30 kill 10 read 20 idle 600
###########################################################
xrootd.seclib libXrdSec.so
sec.protocol unix
sec.protocol sss -c /etc/eos.keytab -s /etc/eos.keytab
sec.protbind * only unix sss
###########################################################
all.export / nolock
all.trace none
all.manager localhost 2131
#ofs.trace open
###########################################################
xrd.port 1095
ofs.persist off
ofs.osslib libEosFstOss.so
ofs.tpc pgm /opt/eos/xrootd/bin/xrdcp
###########################################################
# this URL can be overwritten by EOS_BROKER_URL defined /etc/sysconfig/xrd
fstofs.broker root://eos.aligrid.hiroshima-u.ac.jp:1097//eos/
fstofs.autoboot true
fstofs.quotainterval 10
fstofs.metalog /var/eos/md/
#fstofs.authdir /var/eos/auth/
#fstofs.trace client
###########################################################
# QuarkDB cluster info needed by FSCK to perform the namespace scan
fstofs.qdbcluster grid04.aligrid.hiroshima-u.ac.jp:7777 grid05.aligrid.hiroshima-u.ac.jp:7777 grid06.aligrid.hiroshima-u.ac.jp:7777
fstofs.qdbpassword_file /etc/quarkdb.pass
# Use gRPC?
#fstofs.protowfusegrpc true
fstofs.filemd_handler attr
#-------------------------------------------------------------------------------
# Configuration for XrdHttp http(s) service
#-------------------------------------------------------------------------------
if exec xrootd
xrd.protocol XrdHttp:8001 libXrdHttp.so
http.exthandler EosFstHttp /usr/lib64/libEosFstHttp.so none
http.trace false
# HOST CERTS REQUIRED
#http.exthandler xrdtpc libXrdHttpTPC.so
#xrd.tls /etc/grid-security/hostcert.pem /etc/grid-security/hostkey.pem
#xrd.tlsca certdir /etc/grid-security/certificates/
fi
xrootd.monitor all flush 60s window 30s dest files info user grid01.aligrid.hiroshima-u.ac.jp:9930